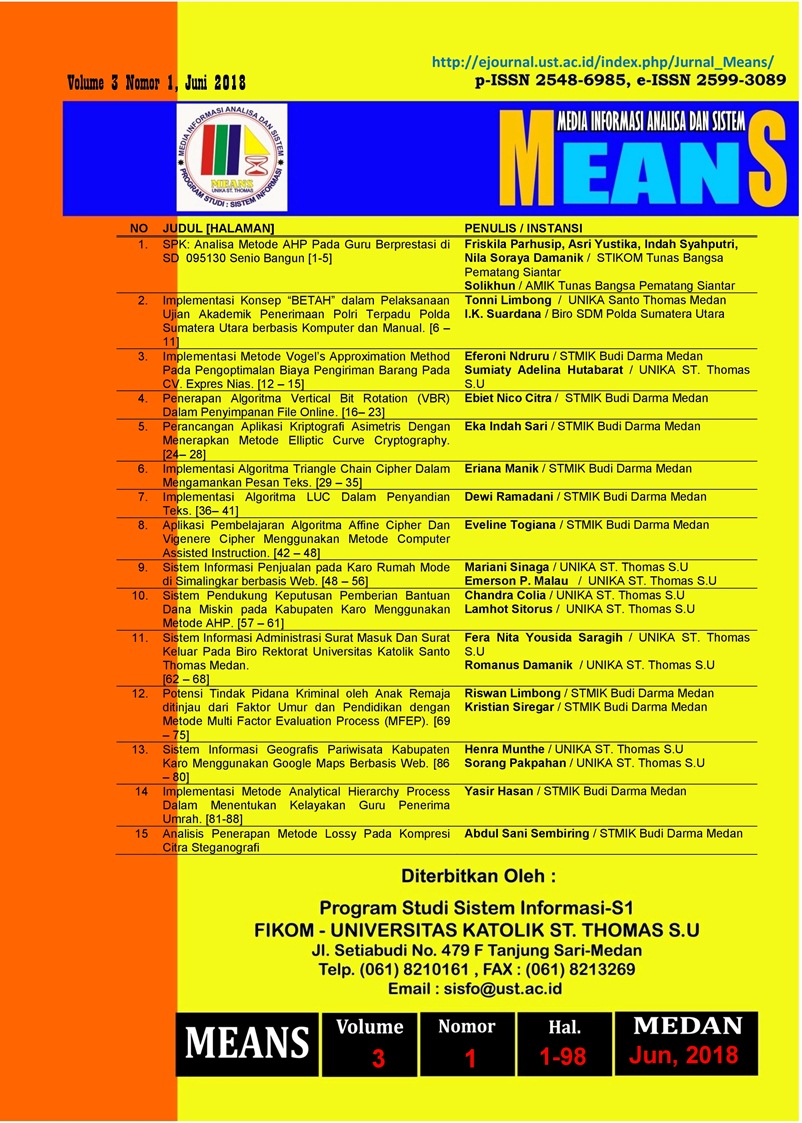
Analisis Penerapan Metode Lossy Pada Kompresi Citra Steganografi
DOI:
https://doi.org/10.54367/means.v3i1.236Keywords:
Lossy, Citra, Kompresi, Steganografi, BPCSAbstract
The internet has become a very important part of communication development in the world. Exchange of information over the internet has many advantages compared to other communication media, especially in terms of speed. But information sent via the internet, security cannot be accounted for. Tapping on confidential information, very often occurs in this communication media. Channels used by the internet are generally not safe channels. By using the lossy compression method, compression can only be applied to images that have similarities to themselves (self similiarity) so that the size of the image gets smaller and saves storage space and accelerates the sending of the image using internet media.References
. Abdul Sani Sembiring, “Analisis Steganografi Pada Citra Terkompresi Dengan Metode Bit-Plane Complexity Segmentation (BPCS), Cemerlang 0216 – 3535, Vol 12/1-117/NOP-DES 2011
. Eiji Kawaguchi and Richard O. Eason. “Principle and applications of BPCS-Steganographyâ€, Kyushu Institute of Technology, Kitakyushu, Japan and University of Maine, Orono, Maine 04469-5708.
. Shrikant S. Khaire and DR. Sanjay L. Nalbalwar (2010). "Review: Steganography – Bit Plane Complexity Segmentation (BPCS) Technique", Department of Electronics & Telecommunication, Dr. Babasaheb Ambedkar Technological University, Lonere, Dist: Raigad, Maharashtra, India. 2(9). 4860-4868.
. Sherin Jabbar and Shaiju Panchikkil. “Lossy Compression Schemes Based On Transforms-A Literature Review On Medical Imagesâ€, Department of Computer Engineering, MES Engineering College, Kuttippuram, Kerala, International Journal of Advanced Information Technology (IJAIT) Vol. 2, No.6, December 2012
. Mulyanto Edy, S.Si., M.Kom. (2009), “ Teori Pengolahan Citraâ€, Jogjakarta : Penerbit Andi.
. Miano and John (1999). “Compressed Image File Format JPEG, PNG, GIF, XBM, BMP†Addison Wesley Longman, Inc.
. Negnevitsky Michael (2002), “Artificial Intelligence : A Guide to Intelligence Systemâ€, Enggland: Addison-Wesley.
. Dony Ariyus (2006),â€Computer Securityâ€,Yogyakarta :Andi Offset.
. http://color-me-club.deviantart.com/art/Zebra-lineart-99491504
. http://www.eclipse.org/articles/Article-UI-Guidelines/Index.html
. http://www.infofotografi.com/blog/2014/06/dynamic-range-bit-depth-dan-color-depth-dalam-sensor-kamera-digital/
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2018 Media Informasi Analisa dan Sistem

This work is licensed under a Creative Commons Attribution 4.0 International License.