Aplikasi Pembelajaran Kriptograpi berbasis Mobile menggunakan Computer Assisted Instruction
DOI:
https://doi.org/10.54367/means.v4i1.310Keywords:
Security, Data, Learning, CAI, MobileAbstract
The source of science is still dominated by books, although with the internet students get information with diverse scientific fields, but actually the information comes from material in the book. To be able to master a material from a book, students must first be able to read and understand well. Nowadays software is growing very rapidly. The world of education has also used software to create interactive learning application methods with multimedia concepts. This can help overcome, the level of difficulty experienced by students, in order to be able to attract student learning interest, so that it can automatically improve the learning process to be more active and effective. Actually this method has been widely used and has good benefits in learning. As for the achievements of this study to assist students in learning and understanding the learning of data security techniques, this is a solution in several learning problems, namely an explanation that is too fast, a conducive atmosphere, time, learning media and student interest.References
I. K. Sudarsana et al., “Paradigma Pedidikan Bermutu Berbasis Teknologi Pendidikan,†Jayapangus Press Books, vol. 0, no. 0, Mar. 2018.
P. Berbasis, K. Pbk, and S. Sunarto, “Pembelajaran berbasis komputer (pbk),†pp. 1–11, 1990.
T. Limbong, E. Napitupulu, and P. Simangunsong, Barita,Nauli, “Learning Application Soft Skill for Facial with Computer Assisted Instruction Model,†vol. 1, no. 4, pp. 561–570, 2018.
M. Y. Rhee, Internet Security : Cryptographic Principles, Algorithms and Protocols. Seoul National University, Republic of Korea, 2003.
R. Munir, “Kriptografi,†Inform. Bandung, 2006.
T. Limbong, P. Manullang, and E. Napitupulu, “Dikte Test Applications (IMLA) Using Computer Assisted Instruction (CAI) Model,†Int. J. Eng. Res. Technol., vol. 6, no. 10, pp. 384–388, 2017.
D. Ariyus, “PENGANTAR ILMU KRIPTOGRAFI Teori Analisis Dan Informasi, Fl,†Yogyakarta CV ANDI OFFSET, 2008.
D. Ariyus, “Kriptografi keamanan data dan komunikasi,†Yogyakarta Graha Ilmu, 2006.
I. Wibowo, B. Susanto, and J. Karel T, “Penerapan algoritma Kriptografi Asimetris RSA untuk keamanan data di Oracle,†J. Inform., vol. 5, no. 1, 2009.
“Kriptografi untuk keamanan jaringan dan implementasinya dalam bahasa Jawa / Rifki Sadikin,†p. 2012, 2012.
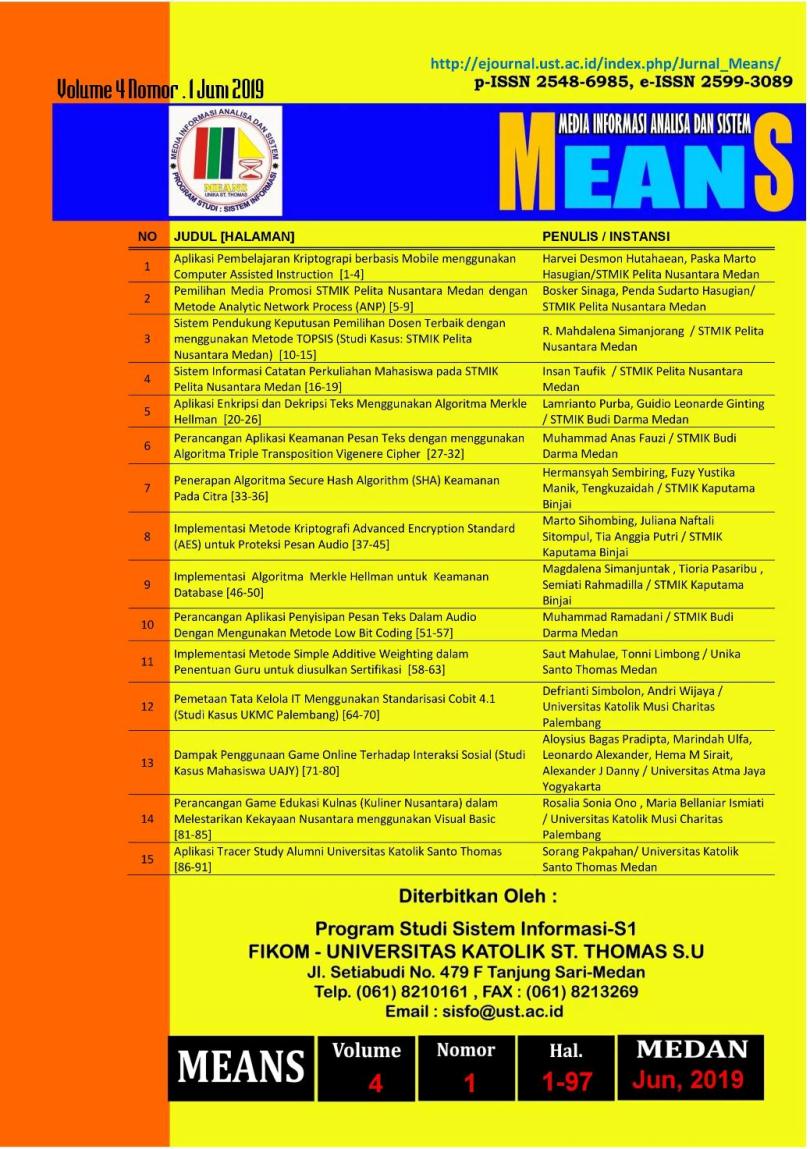
Published
How to Cite
Issue
Section
License
Copyright (c) 2019 MEANS (Media Informasi Analisa dan Sistem)

This work is licensed under a Creative Commons Attribution 4.0 International License.